- Infos im HLRS Wiki sind nicht rechtsverbindlich und ohne Gewähr -
- Information contained in the HLRS Wiki is not legally binding and HLRS is not responsible for any damages that might result from its use -
VPN: Difference between revisions
| Line 8: | Line 8: | ||
https://www.forticlient.com (Windows, Mac) | https://www.forticlient.com (Windows, Mac) | ||
https://github.com/adrienverge/openfortivpn (Linux | https://github.com/adrienverge/openfortivpn (Linux and Mac) | ||
On Fedora, OpenSUSE, and latest Ubuntu openfortivpn is available via packet manager | On Fedora, OpenSUSE, and latest Ubuntu openfortivpn is available via packet manager | ||
On Mac OSX openfortivpn can also be installed via Homebrew | On Mac OSX openfortivpn can also be installed via Homebrew or Macports | ||
== configuration of Fortinet VPN client == | == configuration of Fortinet VPN client == | ||
Revision as of 13:52, 11 December 2018
Access HLRS compute service using VPN
Access to HLRS compute platforms requieres a registration of the clients IP address in the firewall. If the IP address is not static a connection via VPN is recommended.
To use this featrue, please contact your project supervisor and ask him to add the hww-vpn resource in the HLRS user database. Install the Fortigate software on your laptop. The Software could be downloaded on
https://www.forticlient.com (Windows, Mac) https://github.com/adrienverge/openfortivpn (Linux and Mac)
On Fedora, OpenSUSE, and latest Ubuntu openfortivpn is available via packet manager
On Mac OSX openfortivpn can also be installed via Homebrew or Macports
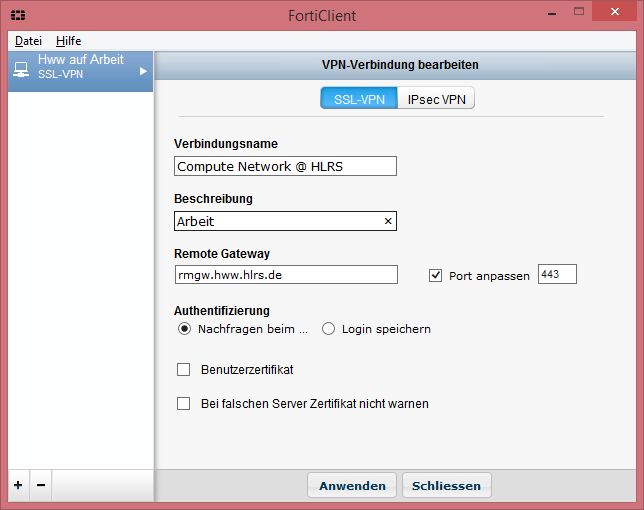
configuration of Fortinet VPN client
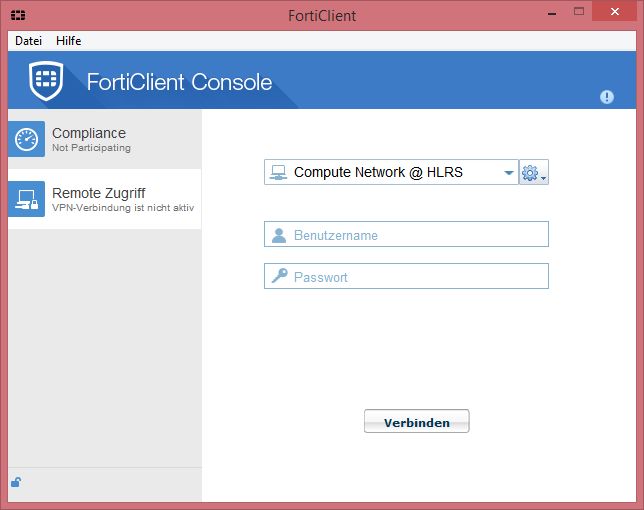
using the VPN
Type your login and password to connect. If this works, you are able to login on the frontend servers using ssh e.g.
ssh -l <your_login> hazelhen.hww.hlrs.de
configuration of openfortivpn
# config file for openfortivpn host = rmgw.hww.hlrs.de port = 443 username = your username # trusted-cert = 06dea2694d2875f82c0c909559f4ba6bb8fd01a3d61e440bf89c22e6222106cb # ca-file = /usr/share/ca-certificates/mozilla/Deutsche_Telekom_Root_CA_2.crt
If your Openssl library is configured correctly and your certificate bundles are installed properly it should not be necessary to explicitly set up the ca certificate. The vpn gateway uses a DFN certificate which is issued below the root ca tree of the German Telekom, one of the CA's trusted by most browsers, the trusted-cert is the digest of the server's certificate which is subject to change every couple of years.